Managed Cyber Security Services
Why Cyber Security Never Quite Leaves Your Mind
If you’re like most business leaders, cyber security sits in the back of your mind.
You know the risks are escalating. You see the headlines. You hear about ransomware, phishing, and data breaches hitting companies just like yours. Yet day to day, you’re expected to trust that everything is under control, without ever really knowing. That uncertainty is draining.
You Don’t Want to Be a Cyber Expert; You Just want to Know That:
- Someone is genuinely paying attention
- Risks are being handled before they escalate
- And if something does go wrong, it won’t land on you unprepared
The truth is, most cyber problems don’t come from negligence. They come from a lack of visibility and unclear ownership.
Real cyber security isn’t about reacting faster when something breaks. It’s about eliminating blind spots altogether. Resilient businesses rely on continuous oversight. Management that treats devices, users, networks, and data as a single, connected system rather than separate parts. When security is proactive rather than reactive, anxiety fades. Decisions feel lighter. And cyber risk stops feeling like an invisible burden you’re carrying alone.
A Cyber Security Partner That Takes Responsibility
Too many businesses are still stuck in reactive security. They use fragmented tools, outsourced monitoring, and providers who only show up after something has already gone wrong. When pressure hits — an incident, an audit, an insurance renewal — leaders are left carrying the risk alone. That’s why we built our Managed Cyber Security services differently to remove uncertainty, restore control, and make security feel contained again.
OhTech is a UK-based IT and cyber security partner supporting small and medium-sized businesses that need clarity, accountability, and real protection. Since 2015, we’ve helped organisations reduce risk, meet compliance requirements, and stay protected as threats evolve. We bring enterprise-level practices to growing businesses, delivered in plain English and aligned to real-world budgets and day-to-day operations.
Our Managed Cyber Security services help business leaders reduce cyber risk, maintain compliance, and gain peace of mind through continuous monitoring, rapid response, and proactive protection. Unlike solutions that focus on tools and noise, OhTech brings device, user, network, and data security together under one managed framework, backed by 24/7 monitoring, in-house expertise, and clear ownership. We don’t outsource responsibility. We own outcomes. With us, there’s no finger-pointing, nor blind spots. You just get security that works in the real world.
Here’s Exactly What You Get
When you order today, here’s exactly what you’ll get with Managed Cyber Security from OhTech.
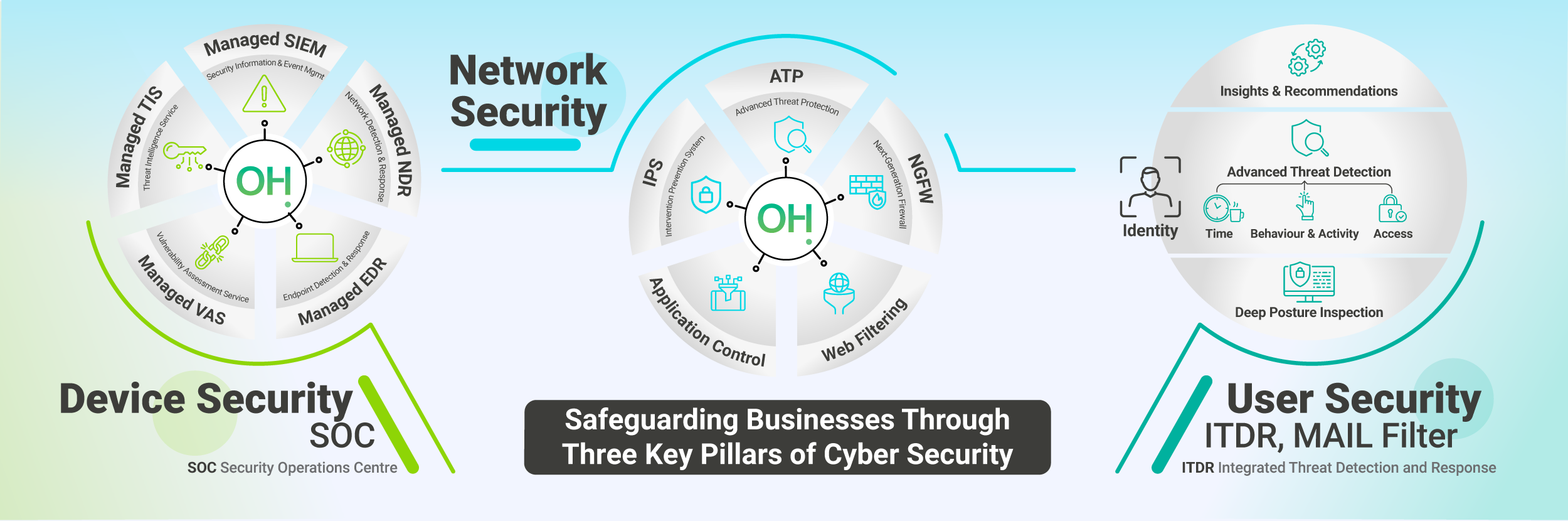
Device Security
Network Security
Safeguard your network from evolving cyber threats with layered protection. From firewalls, intrusion prevention, and secure VPNs to cloud security, segmentation, and Zero Trust access, we protect every connection point. Intertwined with the device 24/7 SOC monitoring and EDR services, we keep your network resilient, compliant, and ready for the future.
User Security
Strengthen your first line of defence. We protect users through strong identity and access controls, multi-factor authentication, role-based permissions, and proactive monitoring. Combined with awareness training and phishing simulations, we reduce human risk, stop credential-based attacks, and keep your organisation compliant.
Endpoint Detection & Response
Managed EDR goes beyond traditional antivirus, detecting and stopping sophisticated threats before they impact your business.
Updating & 3rd Party Patching
Reduce risk and downtime with proactive patching across Windows, macOS, and third-party apps like browsers, Java, and Adobe.
Security Operations Centre (SOC)
Around-the-clock monitoring and threat hunting from our SOC team, ensuring rapid detection, response, and remediation.
Security Information & Event Management (SIEM)
Gain full visibility across devices, networks, and users with real-time log monitoring, threat correlation, and compliance-ready reporting.
Enhanced Encryption
Data Security
Backup & recovery
Data Loss Prevention (DLP)
Ransomware resilience
Protecting data-at-rest & in-transit
Firewalls, IDS/IPS
Strengthen your network security and compliance posture with advanced firewalls and real-time intrusion detection and prevention.
Web Filtering
VPNs & Secure Remote Access
Provide secure, compliant access to your network and cloud services, reducing risk from unsecured connections.
Application Control
Application control ensures only approved software runs on your devices, blocking risky apps and reducing security threats.
Cloud & Application Security
SaaS security (Microsoft 365, Google Workspace)
Cloud workload protection (Azure, AWS)
Application vulnerability management
CASB (Cloud Access Security Broker)
AI-Powered Mail Filtering
AI-powered email filtering stops sophisticated phishing and malware that standard filters often miss, keeping your inbox and your business safe.
Identity Threat Detection & Response
Identity Threat Detection and Response stop account takeovers and insider threats that traditional security tools can’t see, keeping your users and data safe.
Accountable Access Control
Enforce role-based access, track user actions, and demonstrate accountability for compliance and security audits.
Phishing Simulations & Awareness Training
Manage access confidently with complete visibility and accountability.
Governance, Risk & Compliance
Manage access confidently with complete visibility and accountability.

Don’t Leave Cyber Security to Chance
You don’t need to wait for a breach, a failed audit, or a late-night panic to take cyber security seriously.
With OhTech’s Managed Cyber Security, you benefit from continuous protection, expert oversight, and genuine peace of mind. Best of all, you get it without juggling tools, chasing alerts, or carrying the risk alone.
Take the first step today by requesting your cyber audit. It’s quick, straightforward, and designed to give you instant clarity, whether you move forward or not.
Comprehensive Security Reviews & Penetration Testing
As your partner, OhTech provides comprehensive point-in-time audits that enable us to identify and mitigate risks, ensuring a more secure business environment.
Phishing Awareness
Dark Web Scanning
Review the company information available for purchase on the dark web, including personally identifiable information (PII) and leaked credentials that’ve been stolen and cannot be controlled.
Cyber Essentials
Manage infrastructure audits, certification guidance and required remediations for Cyber Essentials and Cyber Essentials PLUS with OhTech as the awarding body.
PenTesting
Test the security controls of your systems, networks and infrastructure through a penetration test to safeguard against external threats.
IR Readiness Assessment
Ensure your teams/provider have a comprehensive Incident Response plan that is easily available to all responders in the event of a breach.
CyberSCAN
Scour for potential threats inside your internal and external networks with our managed vulnerability scanning solution.
GAP Assessments
Gain a detailed analysis of your cyber defences through GAP assessments that align with industry standards (CE, NCSC, ISO 27001, CIS, NIST) and a clear roadmap for improving compliance, evolving security and remediating vulnerabilities.
Infrastructure Assessment
Establish whether attackers can compromise assets like customer or financial data within your business-critical systems.
Application Assessment
Conduct automated and manual penetration tests to assess the security of specific applications and/or code structures.
Web App Assessment
Identify vulnerabilities in business applications accessed via standard web interfaces, whether internally or externally.
Wi-Fi Assessment
Highlight gaps such as unsecured encryption protocols, misconfigurations and weak access controls in your Wi-Fi networks.
Firewall Assessment
Check the configuration of your firewall devices to identify weaknesses or incorrect and sub-optimal setups.
Require Cyber Essentials or Cyber Essentials PLUS?
At Oh-Tech, our goal is to help every business we work with achieve the recognised standard of Cyber Essentials.
We provide both levels of accreditation, tailored to your organisation’s needs.

Cyber Essentials
Cyber Essentials is an online self-assessment questionnaire that assesses your business’ level of cyber security.

Cyber Essentials PLUS
PLUS includes the online self-assessment and an audit of your IT systems completed by our in-house cyber experts and partners.
Concerned About Your Business's Cyber Protection?
That's why we make it easy. Simply request a convenient cyber audit.
Here’s what this changes for your day-to-day.
Walk into audits calm, prepared, confident, and not defensive or rushed.

Request Your Cyber Audit
Complete the form and we’ll be in touch to book a convenient time. We’ll assess your devices, users, network, cloud services and policies, then send a clear, plain-English report showing what’s strong, vulnerable, or at risk. We’ll outline how our Managed Cyber Security services can close the gaps, with no obligation, no disruption, and no pressure.
What You’re Really Investing In
- 24/7 security monitoring by in-house cyber specialists
- Proactive threat detection and rapid response
- Automatic patching and vulnerability reduction
- Clear access control and identity protection
- Compliance-ready security aligned to recognised standards
- Plain-English reporting and accountable support