August 14, 2024
How Much Adversity Warrants Technology Investment?
Businesses deal with all types of problems, and some of them are really serious. Some situations aren’t even problems…yet. When risk is all around you, how can you know when enough is just enough? In today’s blog, we will provide you with some answers to how to flip potential problems into opportunities using technology.
August 2, 2024
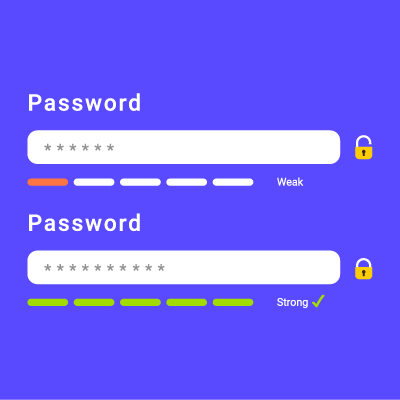
How to Make Bad Passwords Better
Every time you log into an account, you have to enter a password. And we know exactly what you’re thinking: why? Good password hygiene is important, especially in high-profile environments like your business. Passwords play a crucial role in securing your network, so you should know how to build better passwords—if not for your own […]
July 24, 2024
Meta’s Track Record Isn’t Great, Regarding Security
Sometimes, companies don’t take the privacy of their services as seriously as they should, as evidenced by Meta, the parent company of Facebook, WhatsApp, and Instagram. Despite their popularity, these services have had several security and privacy issues over the years. Today, we want to look at some of these services’ most notable privacy and […]
July 22, 2024
Tip of the Week: How to Avoid Social Media Threats in 2024
You can take numerous steps to secure your social media accounts and tighten your privacy settings. Yet, every time you log in, you’re still exposing yourself to a vast stream of information and content. Our civilization has never encountered anything like this before. These platforms are designed to curate content you want to see, encouraging […]
July 17, 2024
Are Your Emails Encrypted? They Should Be!
Email is a centralizing communication tool for most businesses, but what would you do if we asked if your email system was encrypted? Could you give us an honest answer? Encryption is a powerful security measure for networks and infrastructure, so it makes sense to use it for your email solution, too. Here’s what you […]
July 15, 2024
Stay Safe on Social Media with These Strategies
With social media becoming a major part of how society communicates, there’s no better time to discuss how to stay safe while you’re using these significant mediums. Whether you enjoy social media or are against it, there’s no denying that you need to take responsibility to use it. This includes prioritizing your own security.
June 19, 2024
How to Learn from Your Technology Misfires
Dealing with failure can be tough, especially in workplace projects. However, it is crucial to see these failures as opportunities for growth and improvement.
June 7, 2024
Co-Managed IT Can Help Alleviate Some Technology Troubles
If your IT team is overtaken by their responsibilities, we can help. Contact us to learn about our co-managed IT services.
May 17, 2024
Do What You Need to Do to Make Phishing a Non-Issue
If you are a consistent reader of this blog, it will not surprise you that we think of phishing as one of the most significant threats that impact businesses today, regardless of their size or industry. Understanding this threat and implementing effective prevention measures is vital for safeguarding your organization. Let’s go into how you […]